Generate, Sign, and View a CSR With OpenSSL

Razvan Ludosanu
Founder, learnbackend.dev
Published: 2/1/2024
The short answer
A certificate signing request (CSR) is a file containing information about your business and its related website(s) used to request a digital certificate from a certificate authority (CA).
To generate a certificate signing request on Linux and macOS, you can use the following openssl req command:
Where:
- The -new flag is used to generate a new certificate request and prompts the user for relevant field values.
- The -key flag specifies the private key file to use for signing the certificate.
- The -out flag specifies the output filename to write to.
For example, the following command will generate a certificate signing request file named server.csr based on the private key file server.key.
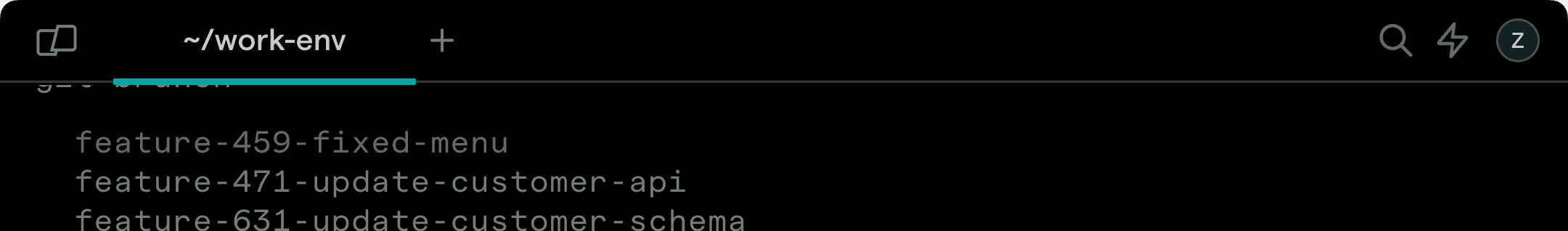
Easily retrieve this command using Warp’s AI Command Search
If you’re using Warp as your terminal, you can easily retrieve this command using the Warp AI Command Search feature:

Entering generate CSR for private key in the AI Command Search will prompt an openssl command that can then quickly be inserted into your shell by doing CMD+ENTER.
Generating a private key file
Before generating a certificate signing request, you will need to generate a private key file, which can be done using the following openssl genpkey command:
Where:
- The -algorithm flag specifies the public key algorithm used to generate the private key (e.g. RSA, DSA, DH, etc).
- The -out flag specifies the destination path of the private key file.
For example, the following command will generate a new private key file using the widely-used RSA algorithm:
Generating a private key and a certificate signing request at once
To generate both a private key and a certificate signing request at once, you can use the following command:
Where:
- The -newkey rsa:2048 flag is used to generate a new private key using the RSA algorithm on 2048 bits.
Generating a certificate signing request with subject alternative names
A subject alternative name (SAN) is a structured way to indicate all of the domain names and IP addresses that are secured by the certificate.
To generate a certificate signing request with subject alternative names, you need to create a configuration file (e.g. csr.conf) with the following structure:
Update placeholder values such as <Country Code>, <Locality>, <Domain Name 1>, etc.
And run the following command to generate the file:
Verifying a certificate signing request
Once generated, you can verify the content of your certificate signing request using the following openssl req command:
Where:
- The -in flag specifies the input file to read from.
- The -text flag prints out the request certificate in text form.
- The -noout flag prevents the output from being encrypted.
- The -verify flag verifies the self-signature on the request.
For example:
Self-signing a certificate signing request
Once generated, a certificate signing request must be signed by a certificate authority in order to be transformed into an actual certificate that can be used to encrypt data.
However, it is also possible to generate a self-signed certificate, which is a certificate that is signed using its own private key.
To sign a CSR, you can use the following openssl ca command:
Where:
- The -in flag specifies the source path of the certificate signing request file.
- The -out flag specifies the destination path of the certificate file.
For example:
Note that, when using a self-signed certificate, warnings may be displayed in the user’s browser as it is not issued by a trusted certificate authority.
Written by

Razvan Ludosanu
Founder, learnbackend.dev
Filed Under
Related Articles
Bash If Statement
Learn how to use the if statement in Bash to compare multiple values and expressions.

Bash While Loop
Learn how to use and control the while loop in Bash to repeat instructions, and read from the standard input, files, arrays, and more.
POST JSON Data With Curl
How to send valid HTTP POST requests with JSON data payloads using the curl command and how to avoid common syntax pitfalls. Also, how to solve the HTTP 405 error code.

Use Cookies With cURL
Learn how to store and send cookies using files, hard-coded values, environment variables with cURL.
Loop Through Files in Directory in Bash
Learn how to iterate over files in a directory linearly and recursively using Bash and Python.

How To Use sudo su
A quick overview of using sudo su

How to use sudo rm -rf safely
We'll help you understand its components

How to run chmod recursively
Using -R is probably not what you want
Run Bash Shell In Docker
Start an interactive shell in Docker container

Curl Post Request
Use cURL to send data to a server

Reading User Input
Via command line arguments and prompting users for input

Bash Aliases
Create an alias for common commands